Enterprise SSO Integration
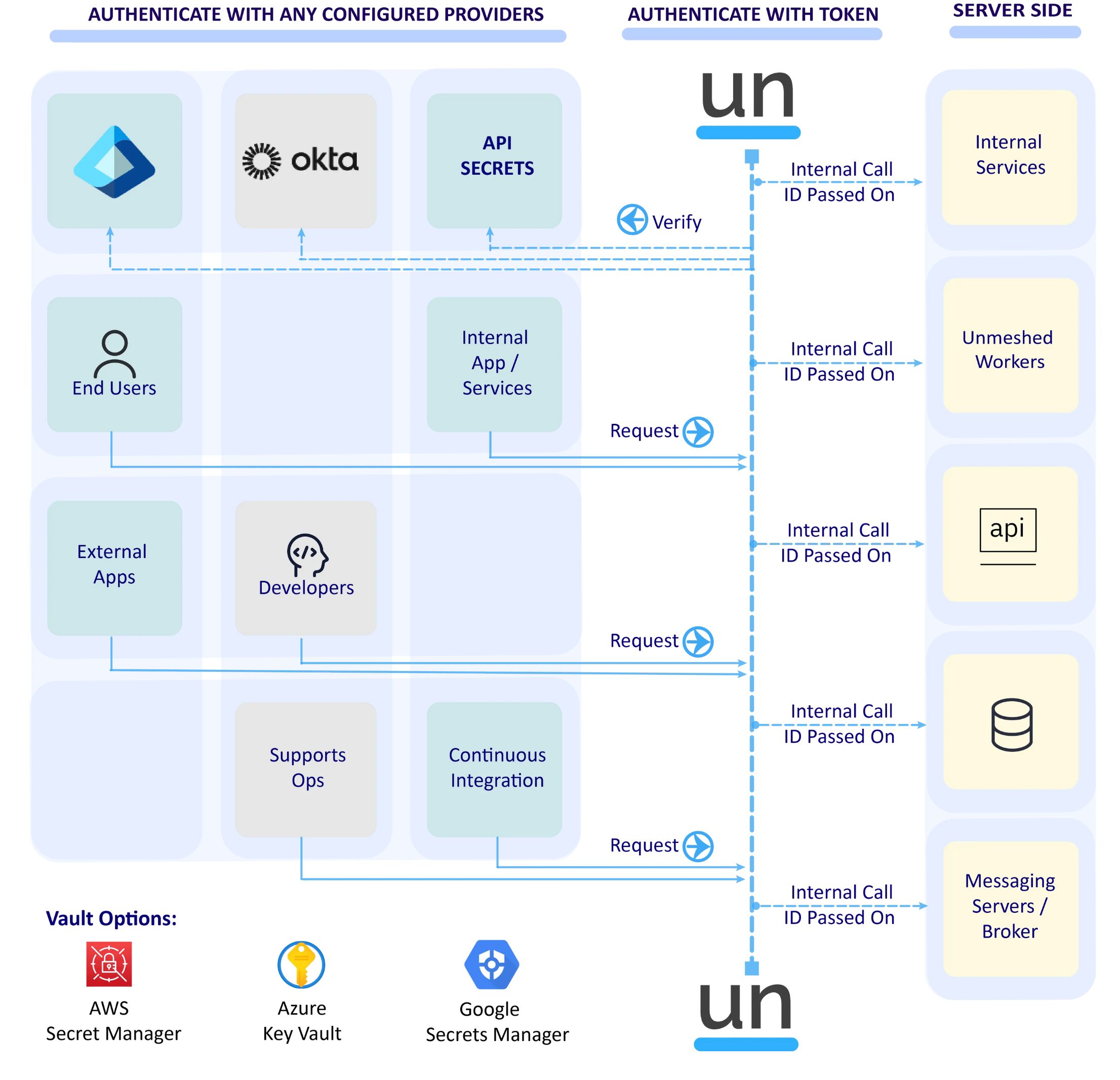
Integrate with your existing SSO and identity architecture while preserving internal governance controls. Unmeshed supports multi-tenant authentication models where internal teams and external API consumers can follow distinct authentication paths.
This is especially useful in Backend-For-Frontend patterns, where endpoint-level authentication behavior must be controlled precisely.